- 1 Minute to read
- Print
- DarkLight
- PDF
Vertica Connection
- 1 Minute to read
- Print
- DarkLight
- PDF
This document will guide you on how to configure and create a Vertica connection in Rivery.
Please follow the next steps in order to create a successful connection.
Create a Rivery database user:
In order to extract data, it's recommended to create a new user in the database for Rivery:
CREATE USER [<RiveryUsername>] IDENTIFIED BY '<myPassword>'
Permit the new user you've created above, to the database:
GRANT USAGE ON SCHEMA '<database>' to [<RiveryUsername>];
More permissions can be found here. We only need a grant of SELECT privileges, so GRANT VIEW is enough.
GRANT SELECT ON SCHEMA '<database>.<schema>' to [<RiveryUsername>];
Connect to Vertica in Rivery:
To connect to your Vertica, you must first set up your database credentials.
Define your Vertica connection:
- In Rivery’s main menu, Go to Connections->Create Connection, or create your new connection in the source, pressing Create New Connection in the Rivers wizard.
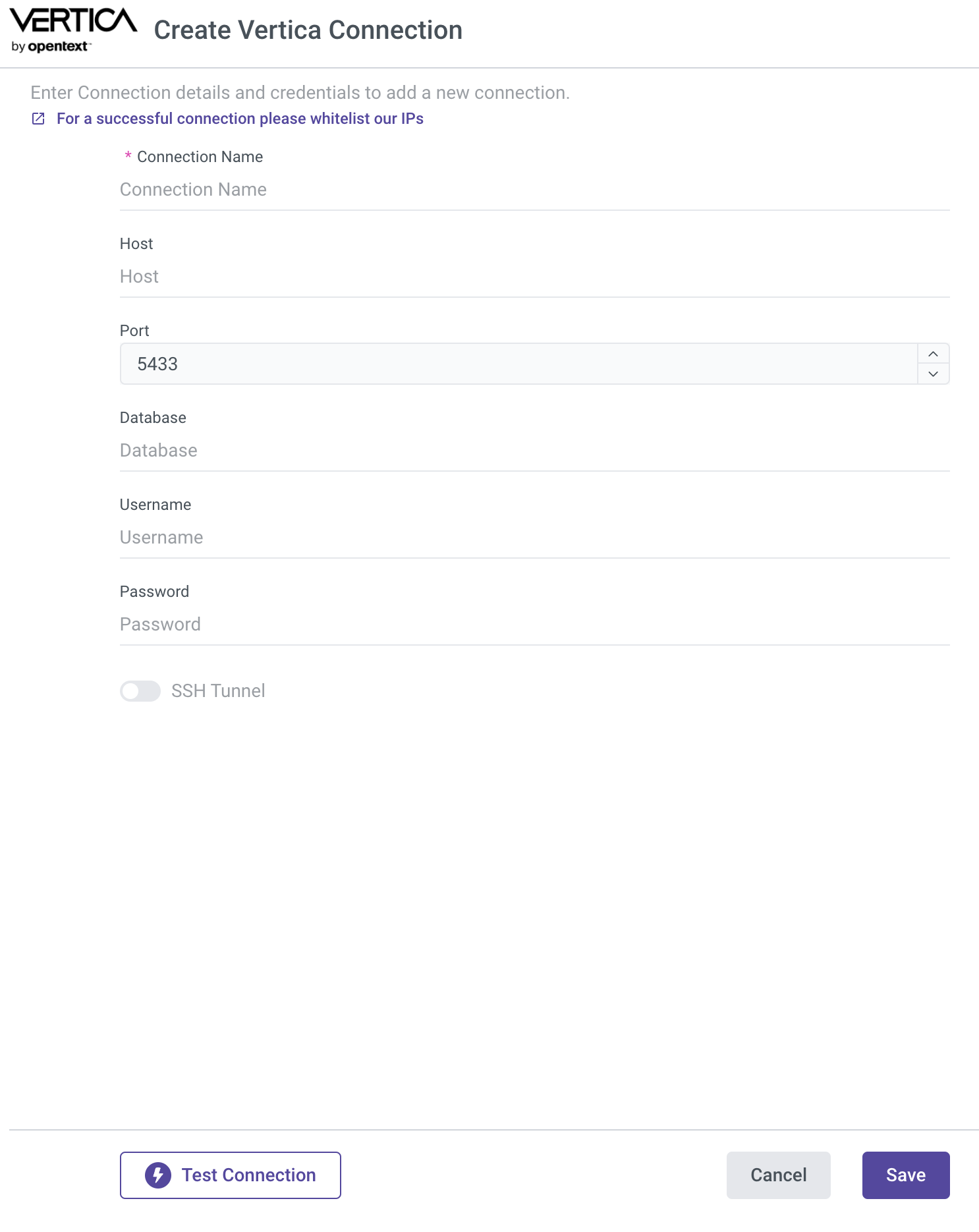
- In the pop-out window, define your credential details: Please be advised about whitelisting Rivery's IPs on your Database Firewall.
3. Define your Host, Port, Database, Username, and Password.
Connecting From Vertica:
Recommended:
Using SSH Tunneling in order of connecting your On-Premise database server with Rivery
Using a hybrid method of data processing, Rivery can connect to on-prem servers. We recommend the use of an SSH Tunneling Method.
To use the SSH Tunneling via Rivery, please configure your SSH Tunnel server in your network. This server will have the ability to get SSH connections from Rivery IPs and will
be able to connect to your database server via the internal IP or address. Rivery connects to that SSH server using a private key.
After you've configured SSH tunneling, you can set it up in the Rivery Connection:
Under the SSH Options section, in the Vertica Connection Pop-up, you can define the following:
- SSH Hostname
- SSH Port (in most of the connection, that should be 22)
- The Username Rivery should connect via the SSH to the server
- Password (optional)
- SSH Pem Key (Recommended)
- And if you have also a Pem Password for that key file.

